Download top and best high-quality free Cybersecurity PNG Transparent Images backgrounds available in various sizes. To view the full PNG size resolution click on any of the below image thumbnail.
License Info: Creative Commons 4.0 BY-NC
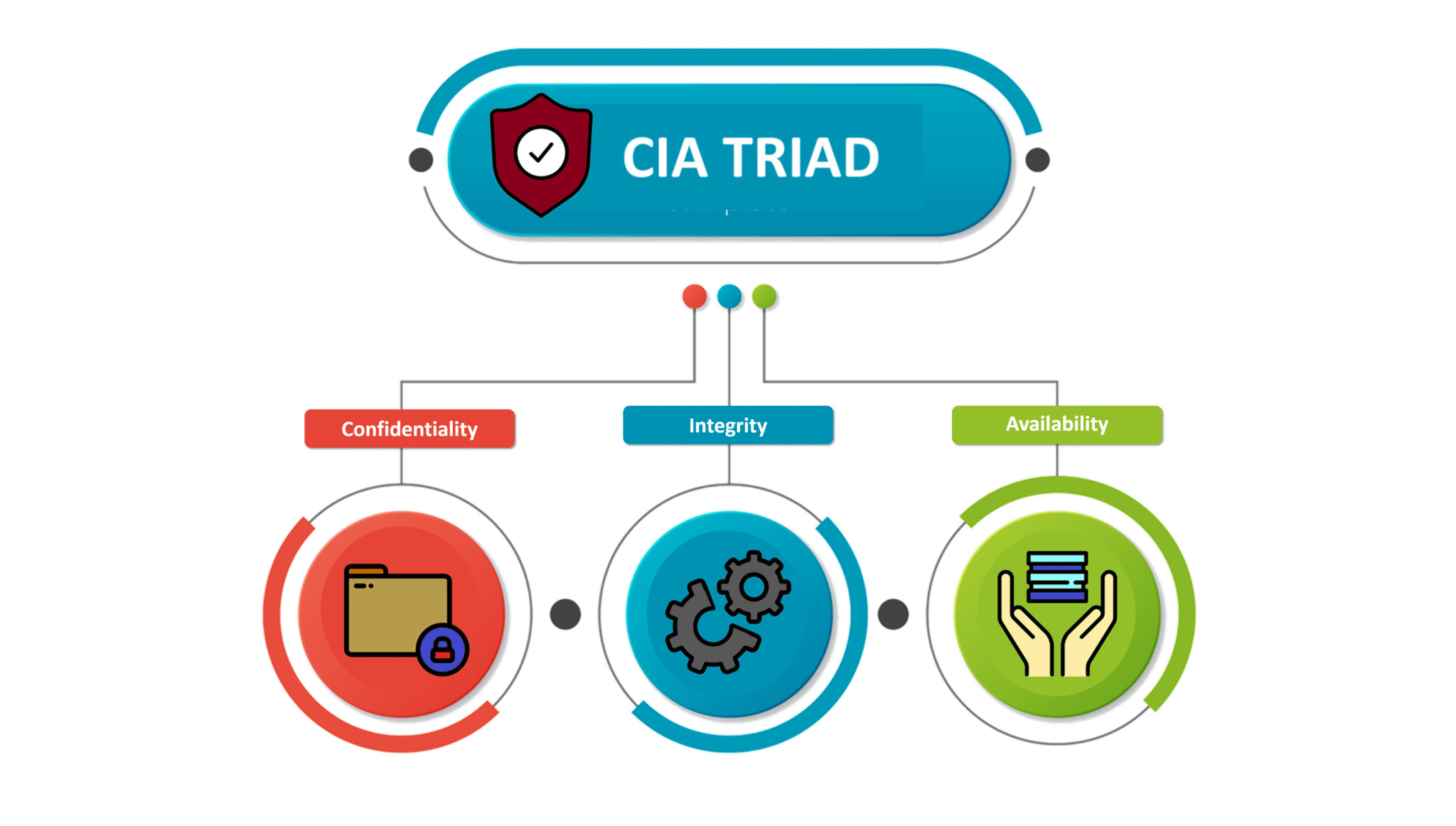
In the early days of cyberattacks, organizations waited for an attack before creating a comprehensive plan and response to the attacker. This attack will render the organization’s network presence unusable for days. Some of the reasons cyberattacks can severely disable networks early in this malicious activity are due to the lack of effort in defending and preventing coordinated efforts between private companies and governments, and lack of effort.
Since the first well-known widespread cyberattack in the mid-1990s, many experts in public and private organizations diligently been studying and working on the issue of cyberattacks. Initially, security companies such as Norton, McAfee, and Trend Micro, etc. approached to tackled this issue with a reactive posture. They knew that hackers/malicious attackers would strike. The goal of what is now called an intrusion detection system (IDS) was to detect malicious attackers before an antivirus, Trojan horse, or worm was used in strike. If an attacker can strike the network, security experts will analyze the code. After the code was analyzed, a response or “fix” was applied to the infected machine. Fixes are called signatures and are downloaded consistently over the network as weekly updates to protect against known attacks. IDS is waiting, but security professionals have a much more sophisticated approach and are evolving as part of the armory.
Security professionals have begun to look at the problem from a precautionary angle. As a result, the cyber security industry has moved from defense mode to attack mode. They were now troubleshooting how to prevent an attack on the system or network. Based on this idea, an intrusion prevention system (IPS) called Snort (2010) was soon introduced. Snort is open source software that combines IDS and IPS and is available for free download. With IDS / IPS software like Snort, security professionals can be active in the cyber security arena. With IPS, security professionals can attack as well as defend, but they are not glorified and do not stop monitoring the work of malicious attackers for creativity, imagination, and innovation. And security professionals who protect the cyber world can be equal or one step ahead of attackers.
Download Cybersecurity PNG images transparent gallery.
- Cyber Security PNG Transparent HD Photo
Resolution: 1024 × 932
Size: 308 KB
Image Format: .png
Download
- Cyber Security PNG
Resolution: 900 × 668
Size: 238 KB
Image Format: .png
Download
- Cyber Security Transparent
Resolution: 346 × 469
Size: 71 KB
Image Format: .png
Download
- Cyber Security
Resolution: 569 × 401
Size: 17 KB
Image Format: .png
Download
- Digital Cyber Security PNG Free Download
Resolution: 980 × 982
Size: 63 KB
Image Format: .png
Download
- Digital Cyber Security PNG Image
Resolution: 650 × 619
Size: 225 KB
Image Format: .png
Download
- Digital Cyber Security PNG Picture
Resolution: 700 × 454
Size: 29 KB
Image Format: .png
Download
- Digital Cyber Security PNG
Resolution: 820 × 792
Size: 275 KB
Image Format: .png
Download
- Digital Cyber Security
Resolution: 860 × 721
Size: 209 KB
Image Format: .png
Download
- Cyber Security Logo PNG Image
Resolution: 860 × 602
Size: 111 KB
Image Format: .png
Download
- Cyber Security Logo PNG
Resolution: 860 × 913
Size: 112 KB
Image Format: .png
Download
- Cyber Security Logo Transparent
Resolution: 840 × 800
Size: 135 KB
Image Format: .png
Download
- Cyber Security Logo
Resolution: 820 × 487
Size: 109 KB
Image Format: .png
Download
- Cyber Security PNG Clipart
Resolution: 860 × 543
Size: 175 KB
Image Format: .png
Download
- Cyber Security PNG File Download Free
Resolution: 840 × 859
Size: 227 KB
Image Format: .png
Download
- Cyber Security PNG File
Resolution: 840 × 637
Size: 129 KB
Image Format: .png
Download
- Cyber Security PNG Free Download
Resolution: 820 × 888
Size: 429 KB
Image Format: .png
Download
- Cyber Security PNG HD Image
Resolution: 2048 × 1162
Size: 123 KB
Image Format: .png
Download
- Cyber Security PNG Image File
Resolution: 1091 × 489
Size: 476 KB
Image Format: .png
Download
- Cyber Security PNG Image HD
Resolution: 528 × 259
Size: 13 KB
Image Format: .png
Download
- Cyber Security PNG Image
Resolution: 820 × 382
Size: 132 KB
Image Format: .png
Download
- Cyber Security PNG Images
Resolution: 730 × 472
Size: 197 KB
Image Format: .png
Download
- Cyber Security PNG Photo
Resolution: 1030 × 617
Size: 232 KB
Image Format: .png
Download
- Cyber Security PNG Picture
Resolution: 860 × 326
Size: 165 KB
Image Format: .png
Download